Mobile App Authentication Technology
The mobile phone authenticators are available in an application: AuthControl Mobile®. Designed to provide users with a flexible way of authenticating, the AuthControl Mobile® app is extremely efficient and without the costs associated with a hardware token.
About the authentication mobile application
There are a number of ways to authenticate by utilising the mobile application (AuthControl Mobile®) including an effortless and effective PUSH notification with Swivel One Touch®, OATH soft token, and a one-time code (OTC) for both Android and iOS operating systems. Both options provide the user with alternative ways to authenticate access to their applications, as part of the multi-factor authentication platform – AuthControl Sentry®.
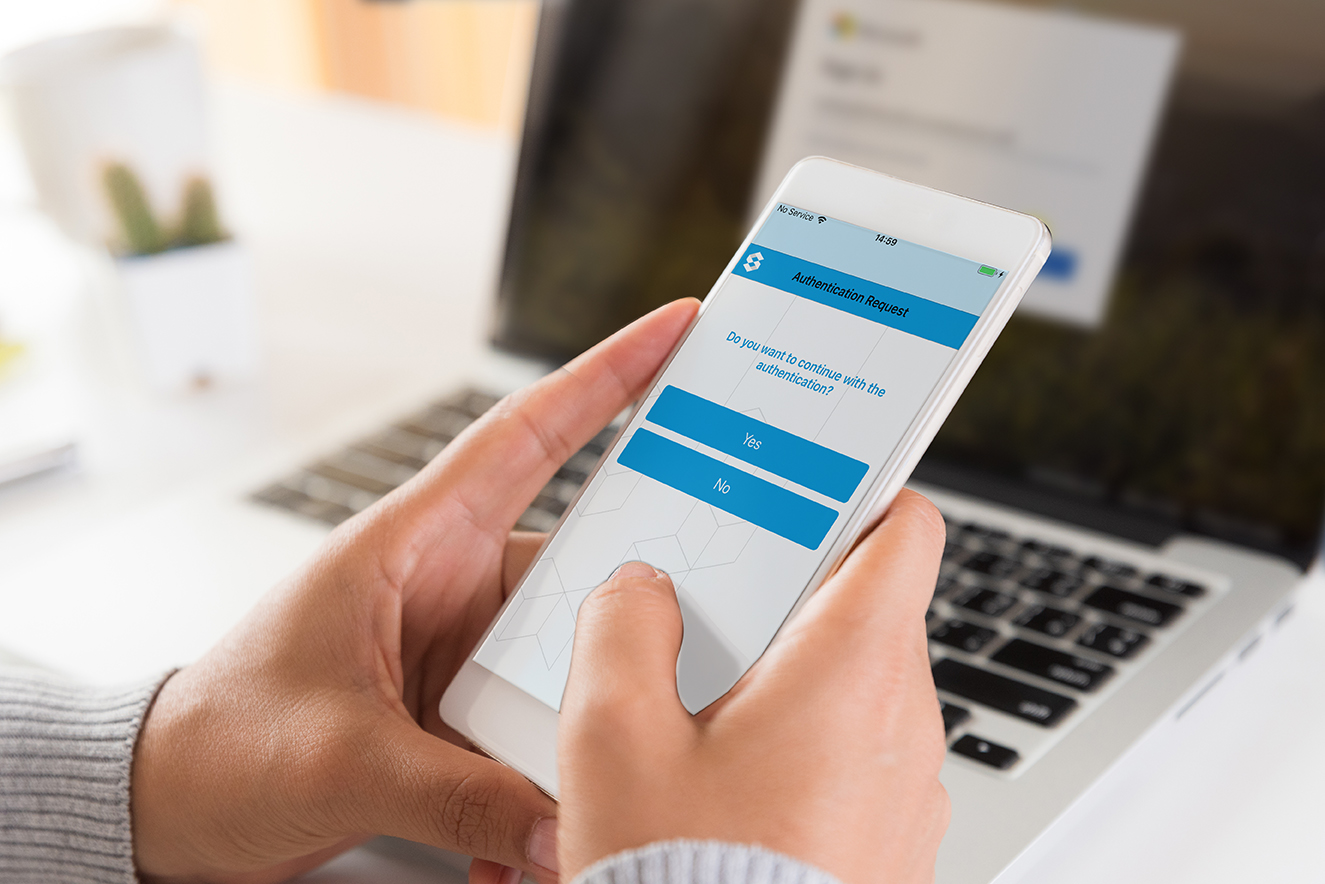
Mobile app: PUSH notification with
Swivel One Touch®
Whether you are working in the office or remotely, the PUSH notification on the mobile app is easy to use and offers a secure way of authenticating.
Simply by pressing a button in the mobile app you can confirm authentication with the notification sent directly to your mobile.
Deploy Swivel One Touch® functionality quickly with minimal configuration required. Access to the authentication factors is easily managed by adding/removing users from specific groups.

Mobile app: One-time code (OTC)
The OTC on the mobile app is an ideal way of generating a security code to authenticate access to your applications.
Each time you are challenged to authenticate, simply use the OTC displayed in the App. As there are 99 codes, the OTC function is versatile enough to be used offline. Once the code has been entered, you will be granted access to your application.
If risk-based authentication is implemented, access will only be granted if you meet the requirements of the risk policies.

Mobile app: OATH
The OATH soft token is a time-based token, similar to the traditional hardware token used to access applications through the VPN. The Initiative for Open Authentication (OATH) compliant soft token on the mobile app provides the user with a six-digit code to authenticate using a one-time code.
Counting from 0 to 60, the OATH token provides a window of opportunity to authenticate with the code supplied, until the time has elapsed when it reaches 60. After this time, a new code will be provided and the timer reset.
An optimal scenario for offline users, this method of authentication is an ideal option for users with a prolonged lack of network coverage because it does not require network coverage to provide the OATH token code to authenticate.

Mobile: short message service (SMS authentication)
As well as authenticating through the mobile application, users can also receive a one-time code (OTC) through their mobile phone or smartphone device by SMS.
Not all users are equipped with a smartphone, but most own at least a ‘regular’ mobile phone that can send and receive a text message to authenticate their login.
PINsafe® protected SMS
To protect the OTC (through SMS) from fraudulent interception, the SMS is protected by PINsafe®. This means the SMS contains a security string of two alphanumerical sequences, and when combined with the user’s PIN provides their OTC – so the true PIN is never exposed.

AuthControl Sentry® Factors
AuthControl Sentry® provides users with the capability of authentication with a range of validation methods. In addition to authentication using a mobile device, users can authenticate using traditional hardware tokens, biometrics (fingerprint), and with image authenticators such as PINpad®, PICpad and TURing.