AuthControl Sentry® Multi-Factor Authentication
The award-winning multi-factor authentication solution
from Swivel Secure
Multi-factor authentication solutions for your business
Deployed in over 54 countries and implemented across enterprises including finance, government, healthcare, education, and manufacturing, AuthControl Sentry® provides organisations with proper multi-factor authentication (MFA). It delivers an intelligent solution to prevent unauthorised access to applications and data. AuthControl Sentry® has the flexibility to support a range of architectural requirements and the ability to ensure maximum adoption, thanks to its variety of authentication factors.

What makes it different?
- Patented PINsafe® technology for ultimate security
- Supports on-premise and cloud for changeable architecture
- A single tenancy and single-tiered cloud solution ensures optimised customisation
- Risk-based authentication and single sign-on as standard
- Integrates seamlessly with hundreds of applications
- Provides maximum adoption with an extensive range of authenticators
AuthControl Sentry® Standard Features
Single sign-on
Single sign-on (SSO) functionality for AuthControl Sentry® provides users with the ability to access all of their applications with a single authentication process. This ensures users can work efficiently without compromising security.
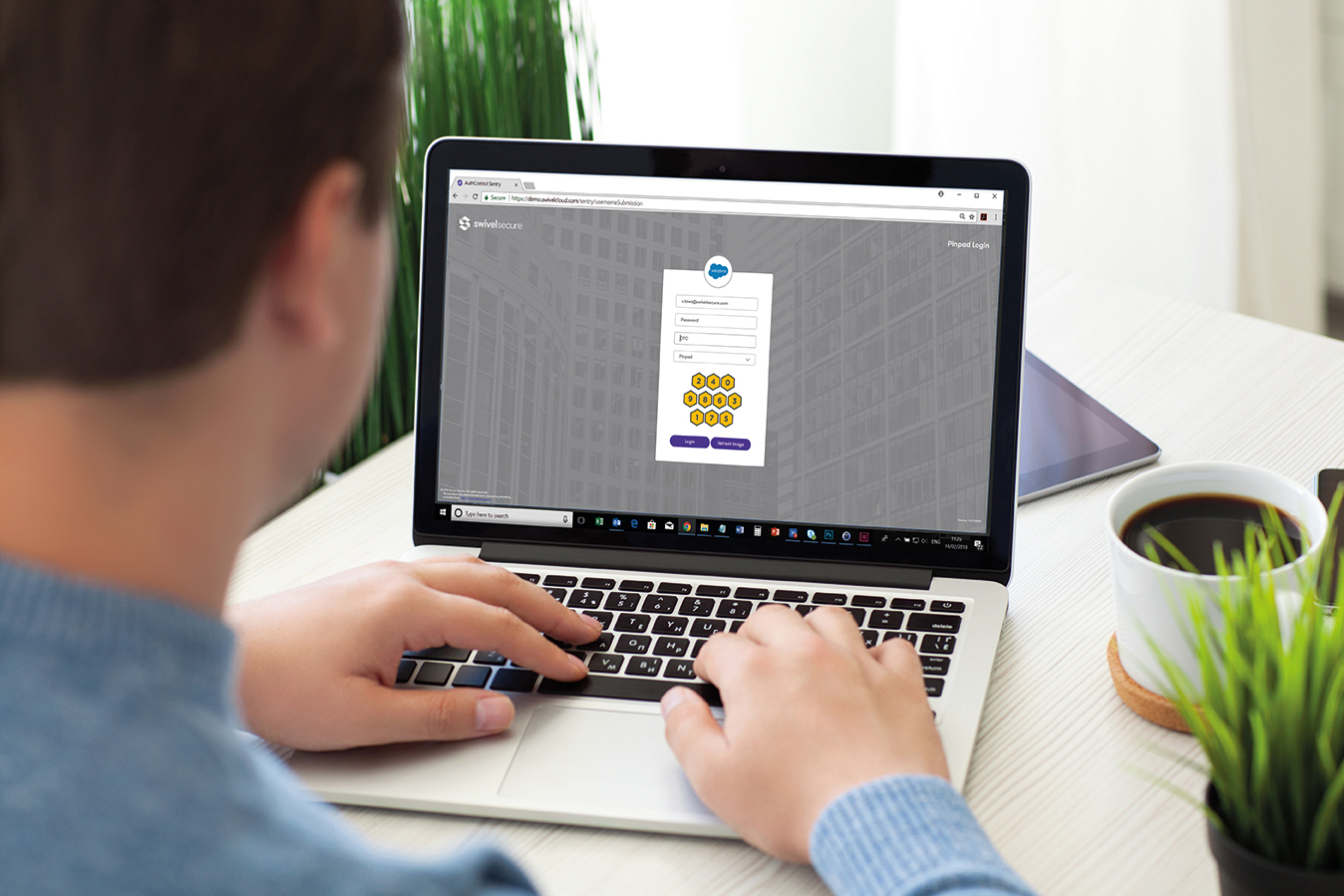
PINsafe® patented technology
PINsafe® is the patented technology behind the image authentication factors PINpad®, PICpad and TURing, part of the range of authentication factors available with AuthControl Sentry®, the multi-factor authentication solution designed to protect organisations from unauthorised access to their applications, networks, and data.
Find Out More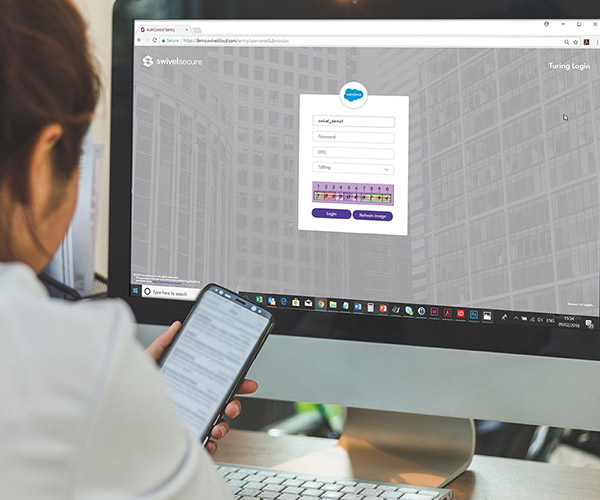
Multi-factor authentication architecture
There are no restrictions with AuthControl Sentry®, designed to authenticate access to applications hosted in the cloud or on-premise and whether the user is a customer, an employee, or a supplier requesting access. Deploy AuthControl Sentry to authenticate a range of stakeholders or use it to authenticate user access to particular applications such as Office 365 or Palo Alto appliances.
On-premise architecture
Active Directory integration - Access internal systems via our Active Directory Agent, a locally installed software application that removes the need to share your Active Directory across the Internet, whilst maintaining user account synchronisation.
Comprehensive administration - With our expert team maintaining the infrastructure, the only thing left for you to manage are the integrations, policies and users. All administration is completed via our simple-to-use, comprehensive graphical user interface.
Single sign-on (SSO) - To make life easy and simplify administration, AuthControl Sentry® provides a seamless and unified approach to authentication. All authentication requests can be routed and controlled via our single sign-on page, based on the risk policies you define.

Cloud based architecture
A fixed IP - Each AuthControl Sentry® customer receives a dedicated fixed IP for their own virtual instance. There is no shared resource, no shared application programming interface, and no shared entry portal.
A dedicated offering - AuthControl Cloud gives you a dedicated virtual machine. There are no shared multi-tenanted options, so you can expect total management and control which means you have the flexibility to configure the solution to meet with your exacting needs.
A private firewall - We offer dedicated and independent firewalls for each customer, allowing tailored security and access control lists.
Examples of AuthControl Sentry® architecture

Architecture for authenticating access to Office 365
In this example, risk-based authentication can be implemented to protect Office 365 from unauthorised access by deploying AuthControl Sentry® as a filter against the ADFS Proxy only and not the internal ADFS.

Architecture for authenticating within a banking environment
This example architecture of AuthControl Sentry® in a banking environment shows how it utilises different resources to request an appropriate level of authentication from the user dependent on the request.

Architecture for integrating with the next-gen firewalls
This example provides an architecture using Palo Alto’s next generation of firewalls. AuthControl Sentry® (with a range of factors) can integrate with Palo Alto firewalls to authenticate users with Active Directory through a single or dual channel.

Optimising security without compromising efficiency
This architectural example is provided for organisations requiring optimum security with fully deployed multi-factor authentication for every user within the business, without compromising the efficiency of carrying out day-to-day activities.

Architecture for integrating with Kemp Web Application Firewall
This example provides an architecture using Kemp’s Web Application Firewall. Kemp technologies together with AuthControl Sentry® delivers efficiency and innovation by empowering customers to
securely deliver applications.
Authentication factors
Swivel Secure provides an extensive range of authentication factors to ensure each deployment provides maximum adoption across your whole organisation. Whether you choose to authenticate by utilising the One Time Code on the mobile app (AuthControl Mobile®), a traditional hardware token or even by using your fingerprint, Swivel Secure’s AuthControl Sentry® provides ultimate security and configurability to suit your business’ security needs. A user is only granted access after successfully presenting two (2FA) or more (MFA) pieces of evidence (factors), proving their identity to an authentication mechanism:
The definition of MFA is based on three principles or factors:
- Knowledge (Something only the user knows)
- Possession (Something only the user has)
- Inherence (Something only the user is)
AuthControl Sentry® Integration and Resources
AuthControl Sentry® is a highly flexible multi-factor authentication solution and its ability to integrate with hundreds of applications and appliance software such as Office 365, Salesforce and Cisco, through RADIUS, ADFS, SAML, and our own proprietary API – AgentXML, makes it one of the best MFA solutions in the market.
You can find in-depth information showing our products, integrations and authentication factors in action, in our resources. It includes whitepapers, datasheets, and videos.