Resources
In-depth Information and Video Resources
We offer a wealth of resources. These include Whitepapers with helpful insights into the data security arena,
Data Sheets to help you learn more about our products and solutions, as well as videos to show our products,
integrations and authentication factors in action.
Find definitions for some of the common terms you’ll find around our website over on our glossary page.
Videos
Salesforce OTC Video
A demonstration video showing the one-time code (OTC) on the mobile app, authenticating access to Salesforce.
TURing Citrix NetScaler Video
A demonstration video showing the TURing image, authenticating access to Citrix NetScaler.
Office 365 PUSH Authentication Video
A demonstration video showing PUSH on the mobile app, authenticating access to Office 365.
Government Cyberattacks Video
A government security solutions video showing the 7 Biggest Government Cyberattacks in the last 7 years.
PINsafe® Demo Video
A demonstration video providing an overview of the patented PINsafe® technology and how it is utilised to provide ultimate security.
Risk-based Authentication Demo Video
A demonstration video providing a comprehensive overview of the Risk-based Authentication process, policies and calculations.
Create a custom MFA chain
A demonstration video showing how easy it is to create a custom MFA chain using the RBA policy engine.
Tips for securing your education network
Andrew Donaldson, regional manager and Adrian Jones, CEO, discuss how education facilities use their IT systems and networks, looking at the common cyber challenges the industry faces and offering their advice for securing an education network.
More Videos
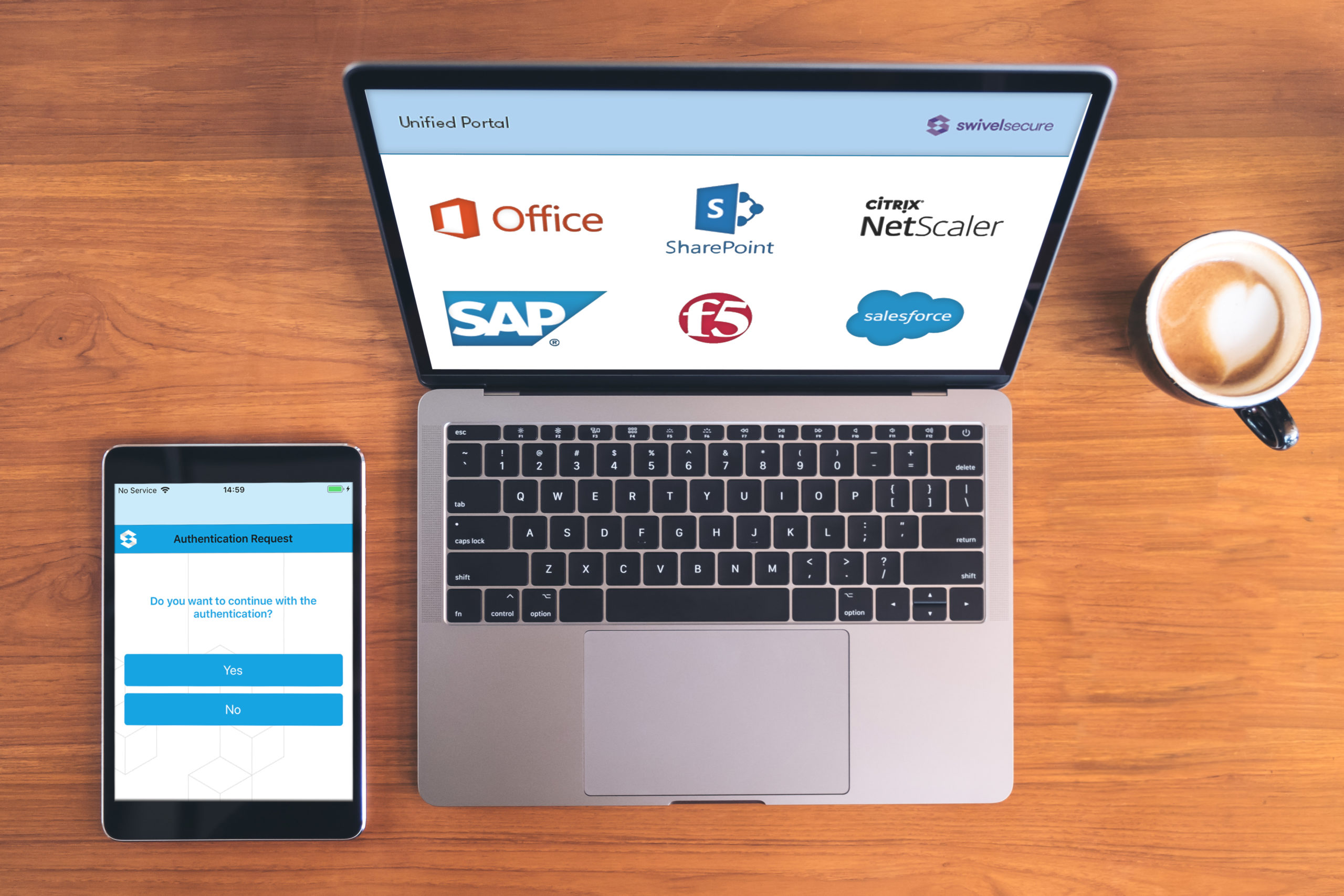
Watch more of our demonstration videos to see how easy it is to authenticate access to all of your applications.
Articles & Updates
Secure users’ access whilst working at home!
Many organisations have had to enable most of their staff to work from home.
This upsurge in remote working has also driven a rise in cyberattacks.
As cyber threats increase, all organisations need to ensure they are protecting their systems against unauthorised access.
AuthControl Sentry® Version 4.1.2
We are pleased to announce the release of AuthControl Sentry® Version 4.1.2! Updates include: User Portal now has Japanese translation, helping to increase customisation and user management. Also, support has been added for our Push feature allowing users more control and easy, secure access using our Mobile App. Learn more about the release of AuthControl Sentry® Version 4.1.2
AuthControl Sentry® Version 4.1.1
We are happy to announce the release of AuthControl Sentry® Version 4.1.1! Updates include the optimisation of our mobile app functionality and its relation with the high latency scenarios. There is an improvement in stability, a better interface, and user experience where users can have more control and a Resource Usage improvement. Learn more about the release of AuthControl Sentry® Version 4.1.1
Three easy wins for deploying an independent multi-factor authentication solution in your organisation
With potentially hundreds of applications utilised within your organisation and some major providers now offering their own independent multi-factor authentication (MFA), processes can become fragmented and inefficiencies can start to instil complacency and reluctance to follow procedures. Read our article on how you could benefit from deploying an independent MFA solution.
AuthControl Sentry® Version 4.1
We are excited to announce the release of AuthControl Sentry® Version 4.1! Updates include a customisable interface, 10 authentication factors which can be configured as a Custom Chain, and PICpad – ideal for multinational companies wishing to set consistent authentication. Learn more about the release of AuthControl Sentry® Version 4.1.
The potential hidden costs of deploying multi-factor authentication in your business
Protecting your business with an authentication solution requires considerable investment. Ensuring you have full visibility of both the initial and the ongoing costs is paramount. Read our article exploring ALL of the potential cost considerations.
Downloadable Resources
Find out everything you need to know about AuthControl Sentry® by downloading our comprehensive brochures
- AuthControl Sentry Overview Brochure
- AuthControl Sentry Full Brochure
- AuthControl Sentry Brochure German
- AuthControl Sentry Brochure Italian
- AuthControl Sentry Brochure Japanese
- AuthControl Sentry Brochure Polish
- AuthControl Sentry Brochure Portuguese
- AuthControl Sentry Brochure Russian
- AuthControl Sentry Brochure Spanish
- AuthControl Sentry Brochure US Letter
- Education: Securing your network against cyber breaches
- Manufacturing: Securing your factories from online threats
- Healthcare: Securing your healthcare organisation from online threats
Learn more about the technology behind our products by downloading one of our Datasheets.
- Swivel Secure 24/7 Maintenance and Support
- Swivel Secure 24/5 Maintenance and Support
- Swivel Secure 8/5 Maintenance and Support
- Integrating AuthControl Sentry with Office 365
- Integrating AuthControl Sentry with Palo Alto
- Integrating AuthControl Sentry with SAP ERP
- AuthControl Sentry
- Swivel Secure Cloud Architecture
- Risk Based Authentication
- SMS Data Sheet
- Mobile App Data Sheet
Find out how we support and protect you with our terms and conditions.
Swivel Secure Ltd. – Cloud Software Services Maintenance & Support Agreement
Swivel Secure Ltd. – Cloud Software Services End User License
Swivel Secure Ltd. – Software License On-Premise End User License Agreement
Swivel Secure Ltd. – Terms and Conditions of Sale
Swivel Secure Inc. – Terms and Conditions of Sale
Swivel Secure – Terms and Conditions of Cloud Service Resale
Swivel Secure – Terms and Conditions for Hardware Tokens
Swivel Secure – Terms and Conditions relating to Bundles
Swivel Secure Ltd. – Terms and Conditions of Deal Registration Program
Swivel Secure – Data Processing Terms
Swivel Secure – Privacy Notice Mobile App IOS
Swivel Secure – Privacy Notice Mobile App Android
Find out more about the Swivel Secure brand including the brand guidelines and logo variations.